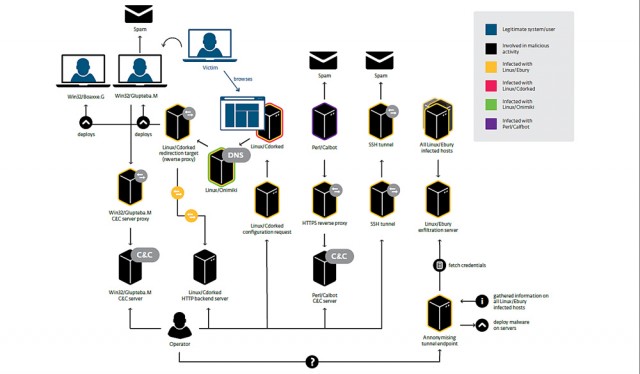
“Until now, publicly known details of the attack were largely limited to its use of a self-injecting rootkit—Phalanx or Phalanx2—to infect kernel.org servers known as Hera and Odin1, as well as personal computers belonging to senior Linux developer H. Peter Anvin. The malware had access to potentially sensitive information stored on the infected machines. A follow-up advisory a few weeks later opened the possibility that still other developers may have fallen prey to the attackers. According to Eset, kernel.org servers were probably infected by a second piece of malware dubbed Linux/Ebury, an OpenSSH backdoor used to keep control of the servers and steal credentials.”
Related posts:
Florida Cops Use SWAT-Style Raids to Check Barbers' Licenses
90+ Arrests of DC Cops Past 4 Years
A record 1 in 5 U.S. households carry student loan debt
Toyota Camry Tops Ford F-150 as the Most American Made Car
Dash cam video exposes cops killing man during routine traffic stop
A Troubling Feature of People Who Seem Nice All the Time
Missouri Cops Ignore State Law, Divert School Funding To Themselves
Chechen Terrorists and the Neocons
Judge Enforces Spy Orders Despite Ruling Them Unconstitutional
New Zealand Regulates -- Not Bans -- Synthetic Drugs
The Final American Revolution: Adam Kokesh vs. Stefan Molyneux
An NSA-Proof Twitter, Built With Code From Bitcoin and BitTorrent
Kidnappers: The Tyranny of Child Protective Services Across the Nation
Supreme Court Screws Small Online Businesses
Will the new gold iPhone lead to an unexpected windfall for Apple in China and India?
