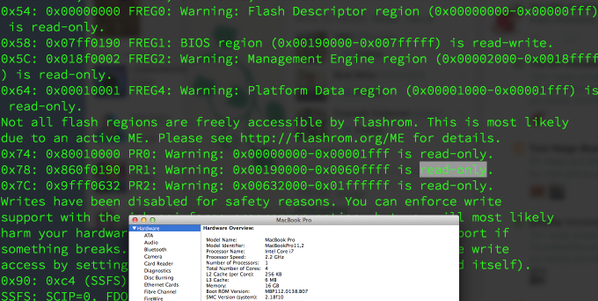
“Macs older than a year are vulnerable to exploits that remotely overwrite the firmware that boots up the machine, a feat that allows attackers to control vulnerable devices from the very first instruction. The attack, according to a blog post published Friday by well-known OS X security researcher Pedro Vilaca, affects Macs shipped prior to the middle of 2014 that are allowed to go into sleep mode. The attack is more serious than the Thunderstrike proof-of-concept exploit late last year. While both exploits give attackers the same persistent and low-level control of a Mac, the new attack doesn’t require even brief physical access. That means attackers half-way around the world may remotely exploit it.”
Related posts:
Judge's Handyman Cops Plea in Georgia Sex, Drugs, Frame-Up
India's pain is UAE's gain - Indian expats buy up gold jewellery
Google Announces $100M Fund For European Startups
A Congressman who Doesn't Cotton to the Constitution
Texas: Court Finds Breath Mints Are Evidence Of DUI
Inevitable Terrorist Attack: Will You Be Manipulated?
Bailout Buffett: The Sage of Solar
US prepares for tank battles in Europe
George Soros Bets $2 Billion on Stock Market Collapse, But Buys Apple
Google, Samsung phones will now receive monthly over-the-air security updates
Jim Rogers on Financial Globalization and Mining Opportunities
Utah Undercover Cops Kill Woman Heroin User
ISIS Is Internet Savvy
'Rookie mistake' in Cryptocat chat app makes cracking a snap
Moneero Turns World's 6.8 Billion Cell Phones into Mobile Cash Wallets
