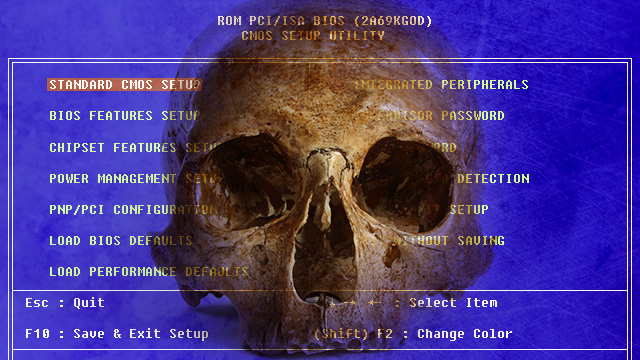
“It’s one thing for researchers in the lab to demonstrate viable firmware-infecting rootkits and ultra high-frequency networking techniques. But it’s another thing entirely to seamlessly fuse the two together and use the weapon in the real world against a seasoned security consultant. A USB stick infecting an array of computer platforms at the BIOS level rivals the payload delivery system found in the state-sponsored Stuxnet worm unleashed to disrupt Iran’s nuclear program. And the reported ability of badBIOS to bridge airgaps also has parallels to Flame, another state-sponsored piece of malware that used Bluetooth radio signals to communicate with devices not connected to the Internet.”
Related posts:
The Closed Door Silicon Valley Meeting with Treasury Secretary Lew
Breakthrough process turns skin cells into protective brain cells
DEA ‘Cold Consent’ Encounters Constitute Federal Stop-and-Frisk
Bill Bonner: Reefer Madness!
Do You Live in a “Death Spiral” State?
84-year-old woman with oxygen tank arrested for drugs
Police databases, key to Trump’s opioid crackdown, push addicts into black market
Android SDK Released - Bitcoin Payment In Your Own Android App
Inflation at the Currency Level
Peter Buffett's Very Public Takedown of His Father, Warren
Extensive Syrian Timeline Exposes Buildup to False Flag
BTCTurk becomes the first Turkish lira-to-bitcoin exchange
Bitcoin exchange opens in Hong Kong
David Gregory Does Some Hard-Hitting News Coverage
Military-Industrial Complex Presstitutes Get SMACKED DOWN By A Real Journalist
