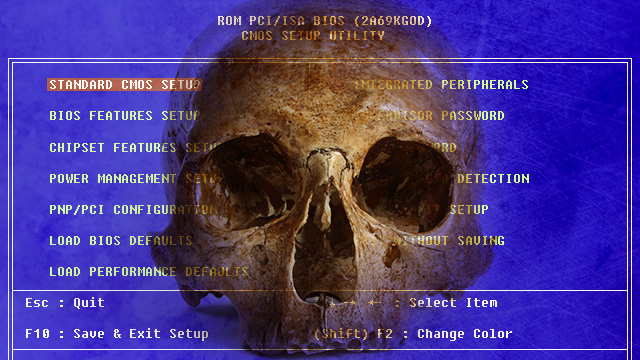
“It’s one thing for researchers in the lab to demonstrate viable firmware-infecting rootkits and ultra high-frequency networking techniques. But it’s another thing entirely to seamlessly fuse the two together and use the weapon in the real world against a seasoned security consultant. A USB stick infecting an array of computer platforms at the BIOS level rivals the payload delivery system found in the state-sponsored Stuxnet worm unleashed to disrupt Iran’s nuclear program. And the reported ability of badBIOS to bridge airgaps also has parallels to Flame, another state-sponsored piece of malware that used Bluetooth radio signals to communicate with devices not connected to the Internet.”
Related posts:
Karl Denninger: Watch for Market Dislocations
'Terms and Conditions May Apply' Trailer
It's Very, Very Easy for Hackers to Steal Your IRS Account
Illinois DOT Busted Over Red Light Camera Spreadsheet
Russia Issues International Travel Advisory to Its Hackers
US National Debt Since 1977 By Congressional Composition
The Forgotten Country Where Profits Beckon
Bank Of England Outs Itself Lying About EU Referendum
Senators Authorizing Syria Strike Got More Cash From Military-Industrial Complex
Adventures in Legal Land with Marc Stevens (2004)
The Little Known Law That Lets Hospitals Shut Down Competition
David Galland: Three Reasons the Case for Gold Remains Intact
Shield Law Defines Journalism So That It Leaves Out Wikileaks & Bloggers
Syria’s Assad to West: ‘I Am Tougher Than Gaddafi’
Public Opinion: Government Healthcare? No!
