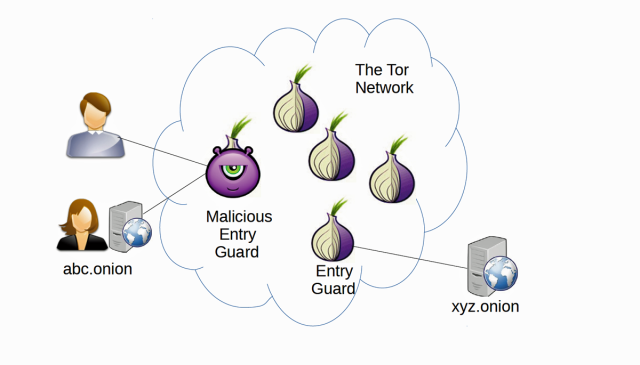
“Computer scientists have devised an attack on the Tor privacy network that in certain cases allows them to deanonymize hidden service websites with 88 percent accuracy. Hidden services allow people to host websites without end users or anyone else knowing the true IP address of the service. The deanonymization requires the adversary to control the Tor entry point for the computer hosting the hidden service. It also requires the attacker to have previously collected unique network characteristics that can serve as a fingerprint for that particular service. The new research underscores the limits to anonymity on Tor, which journalists, activists, and criminals alike rely on to evade online surveillance.”
Related posts:
The “I Thought Bonds Were Safe” Fallacy…
IRS Wants to Be Exempt from Obamacare While also Making the Rest of Us Comply
Anthony Wile: We're Back!
itBit Launches Bitcoin Exchange with $5.5M in Funding
What Was Bradley Manning’s Sin?
Expedia - Vacation Deprivation Key Statistics
Death of Eric Garner Ruled "Homicide by Chokehold"
The biggest scams in Bitcoin history
Pentagon plans to fight ‘War on Terror’ for another 20 years
U.N. Urged to Treat Medical Marijuana As Human Right
Obama 'Hope' poster artist says drones have killed hope
Weed Warrior: Keith Stroup
Florida: Court Approves Detaining Motorists at Toll Booth
L.A. Residents Plead With LAPD On Signs, Shirts: ‘Don’t Shoot, I’m Not Chris Dorner’
Ron Paul's Pod Cast Nation #25 ~ More Gov't Snooping
