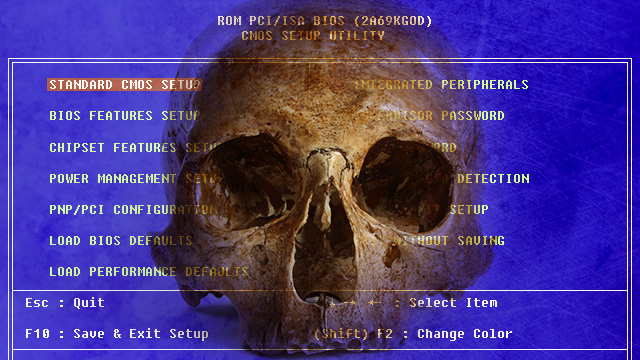
“It’s one thing for researchers in the lab to demonstrate viable firmware-infecting rootkits and ultra high-frequency networking techniques. But it’s another thing entirely to seamlessly fuse the two together and use the weapon in the real world against a seasoned security consultant. A USB stick infecting an array of computer platforms at the BIOS level rivals the payload delivery system found in the state-sponsored Stuxnet worm unleashed to disrupt Iran’s nuclear program. And the reported ability of badBIOS to bridge airgaps also has parallels to Flame, another state-sponsored piece of malware that used Bluetooth radio signals to communicate with devices not connected to the Internet.”
Related posts:
Guantanamo Bay Authorities Ban Solzhenitsyn's 'The Gulag Archipelago'
Your Money or (Five Months of) Your Life
No Way to Stop 3D Printed Guns, Says Homeland Security.
"We're building a domestic army": Marine Corps Colonel speaks out
Decentralised Digital Asset Registers: Mastercoin
Government-Approved Workouts? The Fight Against Fitness Licensing.
US Navy’s first laser weapon cleared for combat, blows up boat and plane
Utah Woman Killed Allegedly “Assassination Style” By Now Disbanding Special Narcotics Unit
The Feds Won’t Stop Terrorism This Way
DEA raids pot shops in Washington state, where marijuana is legal
The Nudge That Will Force Banks to Put More Money Into Treasury Securities
Silver found to be key weapon in fight against antibiotics resistance
The man who stood up to the NSA, Ladar Levison Lavabit founder
Amtrak gets creative, funding 'psychylustro' arts project
Jeff Thomas Responds: Questions on Gold Ownership
