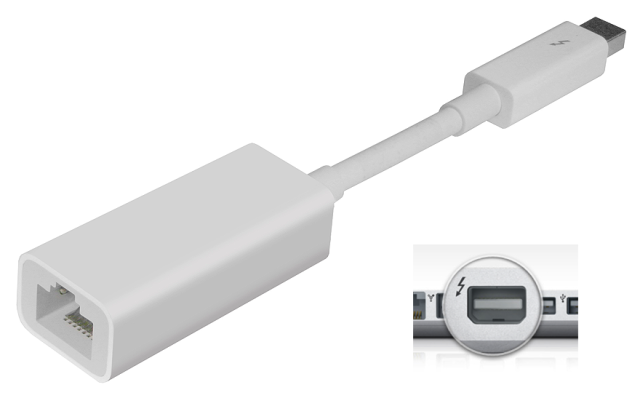
“Dubbed ‘Thunderstrike 2,’ the new proof-of-concept attack still spreads primarily through infected Thunderbolt accessories. But where the original Thunderstrike required a malicious user to have physical access to your computer to work—something sometimes referred to as an ‘evil maid’ attack—the new one can be spread remotely. The malware can be delivered ‘via a phishing e-mail and malicious Web site,’ and once downloaded it can infect connected accessories that use Option ROM (Apple’s Thunderbolt-to-gigabit-Ethernet accessory is a commonly cited example). Once the accessory is infected, the malware can spread to any Mac that you plug the accessory into.”
Related posts:
The Value Of SecondMarket's Bitcoin Trust Just Broke $50 Million
Indiana education commissioner made sure GOP donor’s charter school got top marks
World's Top Hedge Fund Manager On Why You Need to Own Gold
Global warming is ‘no longer a planetary emergency’
Feds seize gold coins worth $80 mln from Pennsylvania family
House Votes to Repeal Sequester, Give Obama Relief
Jury Rejects Charges, but He Still Has to Register As a Sex Offender for Life
UK government publishes 30 tax cheats' photos on Flickr
New Oculus Rift cover shooter is so realistic, players warned not to lean on virtual objects
Silk Road closure reportedly cuts off supply of drug for assisted suicides
Europe Deploys Next Generation Speed Cameras
Small business Obamacare online enrollment delayed a year
The secret Swiss mountain bunker where millionaires stash their bitcoins
Arizona Dispensaries Sold 2.5+ Tons of Medical Marijuana in First Year
John Whitehead: Is the Constitution Even Welcome Here Anymore?
